|
Bitdefender antimalware researchers have put together a checklist of things to do to avoid getting infected with Cryptowall. Cryptowall is a form of ransomware that uses the same encryption and extortion mechanisms as a previous threat, dubbed Cryptolocker. Local files are encrypted using a randomly generated 2048-bit RSA key pair that’s associated with the infected computer. While the public key is copied on the infected computer, the private key can only be obtained by paying for it within an allocated amount of time. If payment is not delivered, the private key is supposed to be deleted, leaving no possible unencrypting method for recovering the locked files. One of the most common infection vectors relies on drive-by-attacks through infected ads on legitimate websites, but it has also been known to infect via infected downloaded apps. Cryptowall infection can be limited and sometimes prevented with: Best practices
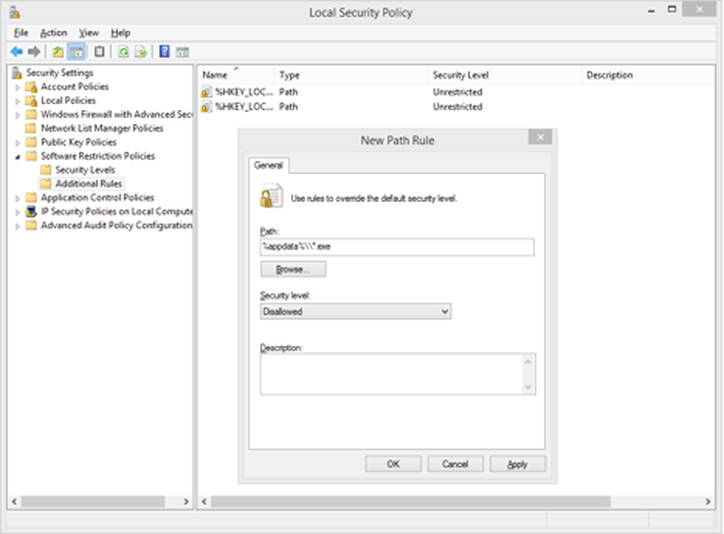
Secondly, aside from these general recommendations, you should also: Enable software restriction policies. System administrators need to enforce group policy objects into the registry to block execution from specific locations. This can only be achieved if you’re running a Windows Professional or Windows Server edition. The Software Restriction Policies option can be found in the Local Security Policy editor. After clicking the New Software Restriction Policies button under Additional Rules, the following Path Rules should be used with “Dissallowed” Security Level: o “%username%\\Appdata\\Roaming\\*.exe” o “%appdata%\Microsoft\Windows\Start Menu\Programs\Startup\\.*exe” o C:\\<random>\\<random>*.exe o “%temp%\\*.exe” o “%userprofile%\\Start Menu\\Programs\\Startup\\*.exe” o “%userprofile%\\*.exe” o “%username%\\Appdata\\*.exe” o “%username%\\Appdata\\Local\\*.exe” o “%username%\\Application Data\\*.exe” o “%username%\\Application Data\\Microsoft\\*.exe” o “%username%\\Local Settings\\Application Data\\*.exe” Setting these mechanisms in place could limit or block Cryptowall.  Article source from Bitdefender LAB. Comments are closed.
|
Protect from RansomwareBuy Bitdefender now RECOMMENDED READINGs
All
|
For BUSINESS: Gravityzone Advanced Business Security
We are a certified Sales Partner (more than 8 years), not principal
Copyright © 2024 We are a Gold Partner of Bitdefender.
Website managed by 57Network.com

 RSS Feed
RSS Feed
