|
A tool to help ransomware victims find which family and sub-version of ransomware has encrypted their data and then get the appropriate decryption tool, if it exists. Are your computer affected by Ransomware? Ransomware has grabbed the world attention ever since 2014. While most ransomware attacks can’t be defeated, Bitdefender constantly creates and updates ransomware decryption tools for families that have either vulnerable encryption algorithms or for which a master decryption key has been leaked. This tool analyzes both the ransom note and the encrypted file samples to identify the strain of ransomware and suggest a decryption tool for the identified family, if such a tool is available. Step 1 Download the BRR tool and save it somewhere on your computer. The latest version is always available here: This tool requires an active internet connection.
Step 2 Run the BDRansomRecognitionTool.exe and allow it to execute if prompted by an UAC alert. Step 3 Read and agree to the End User License Agreement. Step 4 The application has two fields to fill in: Choose the path to the ransom note file or the path to a folder containing encrypted files. You can choose either option, but the tool needs at least one of the pieces of information to detect which strain of ransomware has encrypted your information. If none of the fields are filled in, you cannot proceed any further Step 5 Press Scan. The application gives a warning if the ransom-note path is not filled in, as the detection accuracy is slightly lower in this case. The content of the ransom note is submitted for analysis to Bitdefender cloud. If the user provides any encrypted file, NO file content will be submitted to our cloud, as the tool only analyzes the filename and its extension. If the ransomware family cannot be identified, the user is informed about this. In some cases, multiple families of ransomware display similar features. In this case, the Bitdefender Ransomware Recognition tool displays the possible ransomware families next to an indicator of confidence. Usually the first result is the most relevant and it is displayed with the highest confidence percentage (the one with the highest percentage). If the ransomware has an associated DecryptionTool, a link is provided in the Decryptor column. Good news for system administrators! If you need to run this tool on multiple computers, please use it via command line by passing it the following parameters: -note:RANSOM_NOTE_LOCATION; -test:ENCRYPTED_FILES_LOCATION; Test cases : BDRansomRecognitionTool.exe -note:C:\temp\decrypt_my_files.html; -test:C:\encrypted; BDRansomRecognitionTool.exe -note:C:\temp\decrypt_my_files.html; BDRansomRecognitionTool.exe -test:C:\encrypted; At least one of the parameters above needs to be passed to the tool and end in “;”. Also, any path provided must be absolute. Disclaimer: This tool is developed and offered by Bitdefender, we are listing this additional tool for the purpose of finding solution to decrypt your ransomware-infected Windows based computer. We do not guaranteed for any result and do not take any responsibility or technical support.
Reported by Bitdefender Intelligence, from September 2017 until February 2018,
Ransomware reports have followed a descending curve, while coin miner reports have increased by 130 percent by January 2018. Interestingly, cryptojacking is currently one of the fastest spreading cyber threats, already outranking ransomware’s exposure by a factor of 1 to 100 according to Bitdefender’s intelligence, and is recently displaying targeted behavior, by leveraging fileless techniques and exploits to infiltrate organizations and spread laterally. 
Cryptocurrency mining is a very recent attack wave that spurred in September 2017 and has since been ranked the single biggest cyberthreat of the moment. Crypto jacking is currently one of the fastest spreading cyber threats, already outranking ransomware’s exposure by a factor of 1 to 100 according to Bitdefender’s intelligence, and is recently displaying targeted behavior. Attacks such as WannaMine leverage file less technique and exploits to infiltrate organizations and spread laterally, and even to the point of reaching critical infrastructures.
Ransomware has been notoriously causing serious security concerns, especially when weaponized using government-developed cyber weapons, such as the WannaCry incidents, generating billions of dollars in revenue for cybercriminals.
While cryptocurrency was the main currency for ransomware, everything changed when Bitcoin’s value surged up to $20,000 per unit, making threat actors think of new ways of mining for virtual currencies, as it was more profitable that ransomware. The emergence of browser-based mining clients, such as CoinHive, has spurred a new frenzy of threats, as cybercriminals identified a new, more efferent, and more profitable way generate review.
While the common belief is that only endpoints are facing this mounting threat, threat actors in need of increased computing power and resources have been gunning for data center, as they are more lucrative from a mining point of view. A successful attack on a data center in terms of successfully planning cryptocurrency mining software, can generate a huge revenue for threat actors even it lasts for a mere couple of hours before being detected.
Unfortunately, new cryptojacking attacks embed stealth tactics, which means it takes a long time for them to be detected, while they can cause a huge surge in bills for companies that rely use infrastructure-as-a-service offerings with automatic resource provisioning, such as Azure, AWS or Google Cloud Platform services. For more information about how ransomware and coin miners have evolved over the past couple of months and how data centres are affected, check out the latest “Cryptocurrency Mining Craze Going for Data Centers” whitepaper. To understand the rapid evolution of mining attacks and what risks they can pose for your businesses and infrastructure, particularly if you are running a data center or cloud instances, please watch this webinar hosted by IDC and Bitdefender. Hosted by Alexei Proskura, Program Director, Security, IDC CEE and Liviu Arsene, Senior Global Cyber Security Analyst, Bitdefender, you’ll also gain insights on how to protect your organization from cryptojacking. Sing up for the webinar!
News sourced from Bitdefender
Cybersecurity Industry news By Filip TRUTA A noted Google developer has discovered a troubling flaw in a popular password manager that Windows 10 installs by default. Hackers could get their hands on user passwords via clickjacking and/or malicious code-injection techniques.
Google Project Zero researcher Tavis Ormandy made the discovery while playing around with a Windows 10 virtual machine. Maybe you want to try face recognition rather than setting up a complicated password for better security and privacy protection of your Windows 10 computer. If so, you’re potentially at risk of having your computer unlocked by an attacker by just holding a photograph of you in front of your webcam. More than a third of CISOs (Chief Information Security Officer) have also mentioned the lack of predictability, lack of visibility, lack of control over snapshots and backups, while more than a quarter perceive the lack of granular access over virtual machines and VMs pools as an obstacle during the process. The survey, conducted in May 2017 by Censuswide for Bitdefender, included 1,051 IT security purchase professionals from large enterprises with 1,000+ PCs and data centers, based in the US, the UK, France, Italy, Sweden, Denmark, and Germany. Why conventional endpoint security just don't work for the modern Data Centre? (read the infographic)By Bogdan Botezatu on Nov 17, 2017 |
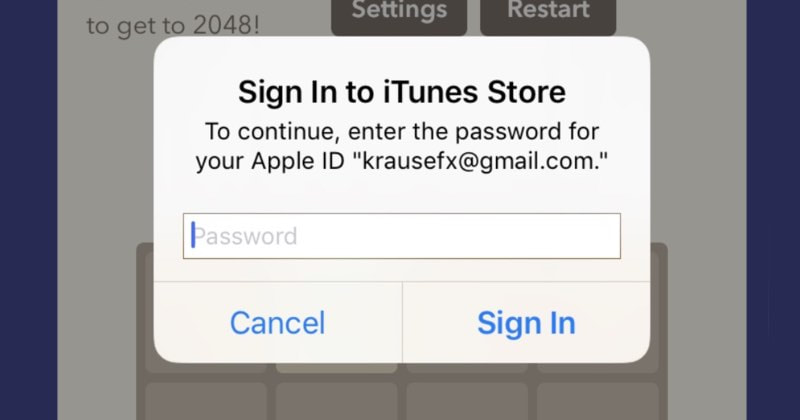
What were the biggest cyber security culprits in the first half of 2017 from a data breach standpoint? Identity theft and poor internal security practices, according to the latest Breach Level Index (BLI) Report by Gemalto. The index, a global database of public data breaches, showed that the first six months of the year had 918 data breaches that led to 1.9 billion data records being compromised worldwide. Compared with the last six months of 2016, the number of lost, stolen or compromised records increased by a staggering 164%, the report said. Much of this was due to the 22 largest data breaches, each involving more than one million compromised records. Of the 918 data breaches during the period, more than 500 (59% of all breaches) had an unknown or unaccounted number of compromised data records. It’s all too easy for a malicious app developer to determine a user’s Apple ID password – just by asking for it.
Developer Felix Krause warns users to be on their guard against password-stealing apps that dupe users into entering their sensitive passwords by using fake login dialogs disguised as legitimate requests from the underlying iOS operating system. The problem lies in the fact that with just a few lines of code, a third-party app developer can pop up a password prompt that looks identical to a legitimate one created by iOS. By Razvan Muresan on Aug 22, 2017 |
Some 90 percent of boards of directors in the US address cybersecurity as a serious risk management issue with severe reputation and financial consequences, while only 8 percent haven’t done it so far, according to a recent Bitdefender survey. Some 60 percent of IT security decision makers in the US say their companies could ‘definitely’ be a target of cyberespionage campaigns using advanced persistent threats (APTs), according to a recent survey by security firm Bitdefender. These complex cyber tools are crafted for high-profile entities and operate by silently gathering sensitive data over long periods. Another 35 percent of respondents say their IT infrastructure could ‘possibly’ be targeted in high-level cyberespionage actions that exfiltrate intelligence systematically. By Bogdan Botezatu on Aug 24, 2017 |
Among the riskier activities enterprises can undertake are merging with or acquiring other businesses—and not just for the financial considerations involved. Mergers and acquisitions (M&A) present a number of cyber security risks that might not even be on the radar screen when merger discussions first begin. A prime example of cyber security risk with such a transaction comes from the recent acquisition of Yahoo Inc. by Verizon. In September 2016 Yahoo announced that a recent investigation by the company had confirmed that a copy of certain user account information was stolen from the Yahoo’s network in late 2014. Some referred to the incident as one of the biggest data breaches of all time. Based on the investigation, the company said it suspected that information associated with at least 500 million user accounts was stolen. At the time, Yahoo was in the midst of being acquired by Verizon. The deal was eventually completed in June 2017, but news of the data breach led to some speculation about whether the transaction would go forward. Data breaches and other attacks by cyber criminals can happen to companies at any time. When it happens during a merger or acquisition, however, that can complicate things significantly. |
Protect from RansomwareBuy Bitdefender now RECOMMENDED READINGs
All
|
For BUSINESS: Gravityzone Advanced Business Security
We are a certified Sales Partner (more than 8 years), not principal
Copyright © 2024 We are a Gold Partner of Bitdefender.
Website managed by 57Network.com


 RSS Feed
RSS Feed
